In This Article
What is Memory Protection?
Memory protection refers to securing the computer memory, either at the software or hardware level to prevent unauthorized access to it by any computer process.
Technically, it is the practice to enhance security of memory by following different additional processes such as protection of executable space in the memory and layout randomization of the address spaces.
KEY TAKEAWAYS
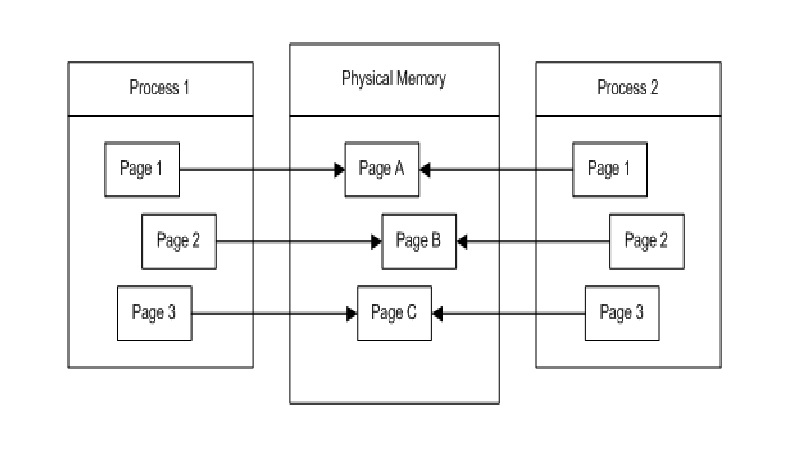
- Memory protection typically refers to the process which prevents unauthorized access to the memory allocated to one program by another.
- This is essential in the multitasking setting where interference between two programs is a common occurrence.
- There are different methods to ensure the protection of memory.
- The efficiency of memory protection, however, depends on the operating system and therefore may vary.
- The level of protection offered depends on the close adherence of the system to the code of minimum privilege.
Understanding Memory Protection
The act of securing the memory to make sure it is not accessed by any unauthorized process is called memory protection. It can be done both at the hardware and the software levels.
The concept of memory protection is not new. In fact, it was implemented for the first time in the 1970s and 1980s.
However, it did not gain steam and was not embraced as a useful computing practice until the 2000s.
Nowadays, memory protection is an integral part of almost every operating system (software level) and CPU architecture (hardware level).
Ideally, different types of memory protection techniques are followed by different operating systems, and that is why their efficiency may vary. Different operating systems that implement this protection technique include:
- Unix and Unix-like systems such as Linux, Solaris, macOS, BSD, GNU Hurd, and iOS
- Plan9
- Inferno
- OS/2
- RISC OS
- Microware OS-9
- Microsoft Windows
- Atari MultiTOS
- Pharos
In short, almost all operating systems available on the market today support some form of memory protection.
However, it has become a more sophisticated technique today mainly due to the advancements in technology.
It can now offer tighter controls over different applications.
There are different methods followed for memory protection, such as:
- Memory protection by using keys or codes to offer page-based protections
- Memory protection by using rings in a hierarchy
- Capability-based protection
- Memory protection by using masks during paging
- Memory protection by using segmentation
- Memory protection by using simulated segmentation
- Memory protection by using dynamic tainting
Why is Memory Protection Important?
There is an immense need to protect your memory because it will prevent a process from accessing any memory space that is not allocated. In other words, it will prevent the software from gaining control over a large amount of memory.
Ideally, with proper memory protection a lot of adverse situations can be avoided. These include any potential and significant damage caused to the system as well as other software programs installed in it.
With proper protection of the memory, you may also be able to identify harmful applications and malicious software that may later affect the performance of the operating system and the computer as a whole.
It also prevents the possibility of any erroneous data transmission, or, in some specific situations, it may also result in the loss of the stored data in the memory during the execution of a program due to specific conditions such as:
- Breakdowns or failures in the equipment
- Inefficient operation of the supervisory program
- Errors by users and programmers
- Intentional or accidental interference
This will increase the efficiency of computer operation because a properly protected, organized and managed memory will result in:
- Reduced search errors
- Lower time losses
- Prevent unauthorized write accesses
- No repeated computations
By preventing unauthorized access, memory protection will, in turn, prevent hardware faults such as:
- A segmentation
- A storage violation
- An abnormal termination of a process
In short, memory protection is important for simultaneous solutions of different issues, latent or obvious, in a computer in a real-time-sharing system.
It will help multiple users when they use program archives and libraries belonging to different users or for the real-time operations of numerous on-line units.
Conclusion
Memory protection is the practice of preserving the contents of the memory and preventing any unauthorized access to the space.
It is integral in hardware and software levels and typically useful in multitasking settings but its efficiency may vary according to the operating system used in the computer systems.
